Too Slow, Too Late?
Security analysts are bombarded with hundreds of alerts per day, resulting in a significant time gap between incident detection and the start of an investigation. In cases where containers or other ephemeral resources have been compromised, security teams often miss the opportunity to understand what happened. By the time the analyst is ready to investigate, the server has been nuked, the evidence is gone, and it's too late.
Every Piece of Data at Your Fingertips.
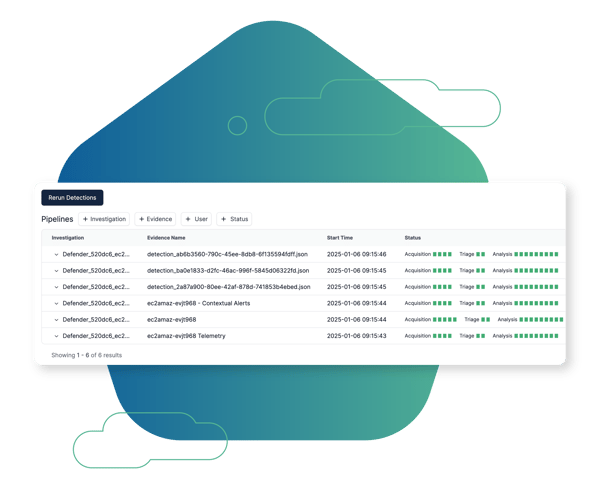
Get Answers. Every Time.
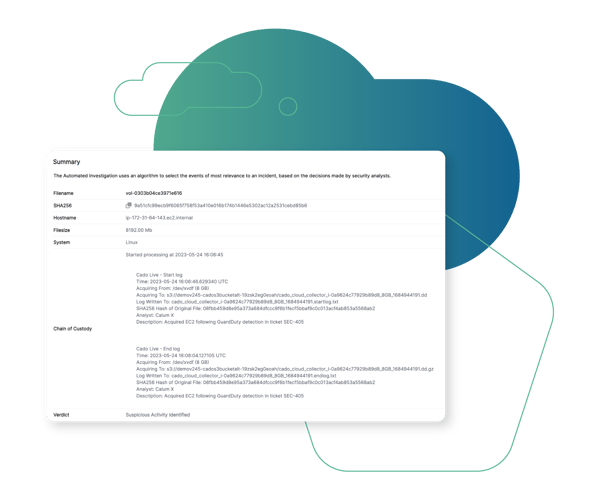
Full Chain of Custody
Chain of custody is handled completely autonomously behind the scenes, and does not require any input from the users. This saves analysts time, enabling them to focus on the investigation itself.
Browse Other Use Cases
Explore other ways security teams are using the Cado platform to advance their mission.
Cross Cloud Investigations
Investigate incidents identified in AWS, Azure, and GCP in a single pane of glass.
Container & K8s Investigations
Perform container investigations in environments including EKS, AKS, GKE, and Kubernetes.
SOC Triage
Automate acquisition of endpoint resources to gain immediate event insights and facilitate quick escalation.
SaaS Investigations
Analyze SaaS logs alongside other critical sources to investigate compromises such as Business Email Compromise (BEC).
Cloud Detection & Response (CDR)
Marry threat detection with automated forensic collection and investigation to expedite response to cloud threats.

The Cado Advantage
Cado Security is helping organizations around the world achieve results.








