IR Success with Cado Security
The Cado Platform is a single solution for cloud threat detection, investigation, and response, providing broad coverage across multi-cloud and container environments. The Cado Platform is the only tool with the ability to perform automated full forensic captures as well as utilize instant triage detection methods - so security teams can quickly identify the true scope and impact of malicious activity. Response actions can then be taken manually to ensure cloud threats are contained around the clock.
The Cado Platform for IR
Attacks are surging in cloud environments. This complexity makes detecting and responding to threats extremely challenging, and having the ability to quickly detect, investigate, and take action is critical to a robust incident response program.
Understand the Risk
With visibility beyond what a traditional detection solution provides, security teams can better understand and manage cloud risk.
Reduce MTTR
Cloud-native means security teams can apply cloud speed to the end-to-end IR process, drastically reducing mean-time-to-respond (MTTR).
Close Skills Gap
By automating where we can, individuals of all levels can perform incident response in the cloud - even in multi-cloud environments.
Top Cado Use Cases
See how security teams are using the Cado platform to close the cybersecurity skills gap.
Cross Cloud Investigations
Respond to incidents identified in AWS, Azure, and GCP in a single pane of glass.
Container & K8s Investigations
Perform container investigations in environments including EKS, AKS, GKE, and Kubernetes.
SOC Triage
Automate triage acquisition of endpoint resources to gain immediate event insights and facilitate quick escalation.
SaaS Investigations
Analyze SaaS logs alongside other critical sources to investigate compromises such as Business Email Compromise (BEC).
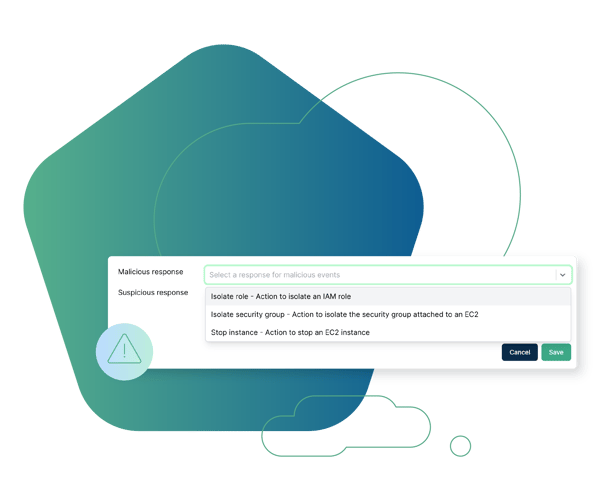
Cloud Detection & Response (CDR)
Marry threat detection with forensic context to expedite response.
Evidence Preservation
Ensure evidence residing in ephemeral environments is immediately captured and preserved before it disappears.

“I can now confidently say I know what's going on in my cloud.”
Cyber Security Incident Response Manager
Global Media Company

“The fact that we no longer have to manually request access to a potentially compromised system via our cloud team is a game changer.”
Incident Response Lead
Large Financial Institution











