SecOps Success with Cado Security
Cado Security revolutionizes how SOC teams approach alert triage, investigation, and incident response. The Cado Platform supercharges your SOC by automatically acquiring data from all your systems, cloud, on-premise, and SaaS apps. This dataset is distilled down into key events to provide your analysts with enhanced focus, allowing them to make confident decisions at speed.
The Cado Platform for SecOps
Today's SOC teams are tasked with making split second decisions on behalf of entire organizations, often without the full picture. This mission-critical group needs information at a moments notice, seamlessly integrated directly into their existing systems and workflow.
Understand the Attack
Automatically surface key malicious activity, root cause, incident scope, and the complete timeline of events.
Respond Immediately
Apply cloud-speed to the end-to-end IR process, drastically reducing mean time to respond (MTTR).
Full Context
Perform automated full forensic captures as well as utilize instant triage collection methods - leaving no stone unturned.
Workflow Automation
Streamline processes, enhance the accuracy of threat detection, and allow analysts to focus on higher-value tasks.
Top Cado Use Cases
See how security teams are using the Cado platform to close the cybersecurity skills gap.
Cross Cloud Investigations
Respond to incidents identified in AWS, Azure, and GCP in a single pane of glass.
Container & K8s Investigations
Perform container investigations in environments including EKS, AKS, GKE, and Kubernetes.
SOC Triage
Automate triage acquisition of endpoint resources to gain immediate event insights and facilitate quick escalation.
SaaS Investigations
Analyze SaaS logs alongside other critical sources to investigate compromises such as Business Email Compromise (BEC).
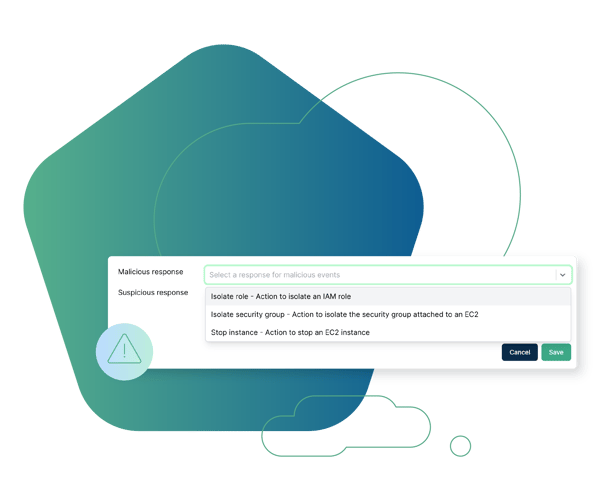
Cloud Detection & Response (CDR)
Marry threat detection with forensic context to expedite response.
Evidence Preservation
Ensure evidence residing in ephemeral environments is immediately captured and preserved before it disappears.

“I can't believe I'm now able to process a 500GB disk in just a few hours.”
Security Operations Manager
Global Gaming Company











